Question like how protected your data is, whether it is secured or not, has anyone else got access to your data are likely to be popping into your head ever since you decided to hire Question like how protected your data is, whether it is secured or not, has anyone else got access to your data are likely to be popping into your head ever since you decided to hire cloud computing service providers. These are the questions which may not let you sleep at night since every single detail ranging from bank account passwords to the contents of your accounts department will be certainly stored in there. Security in cloud computing would be your first concern. Now the only help you can get here is by helping yourself, which can be done by learning the internal security schema.

Theft or loss of data
You may be suspicious of storing your data into something, which doesn’t exist physically but that is also an advantage that makes your data invisible to the naïve user attempting to breach your data.
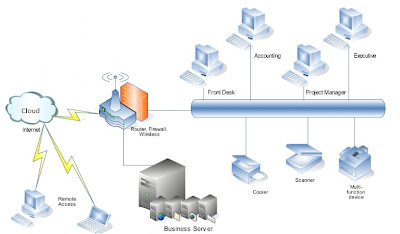
Your provider will enable you to store your data in multiple servers who are again supported by a series of firewalls. No doubt hackers are born every day; cloud computing professionals claim of giving the best security systems that will prevent infiltrators gaining access even to the first-tier security level. In fact, research and development programs are conducted on a regular basis to remain updated to the recent threats and devise techniques and solutions to maintain security in cloud computing.
Corporate these dates are very concerned about their data against competitors who are also finding ways to harm their business in every possible way. Providers must ensure that no data is accessible to persons other than their owners in any mishaps.
Common issues of Security in cloud computing like the site scripting, SQL objections, cross-site request forgeries are common occurrences in cloud computing.
Physical protection of servers is also superbly controlled through locked server rooms; strict security protocols, regulated authorized access and cautious physical handling of hardware.
System Failures
In case of calamity where your server crashes, data recovery and work resuming are very quick and accurate. No page alterations or loss of history will be encountered. Within minutes, you will be seeing the page you were previously working on.
Cloud computing strives to deliver you the best service and work experience that creates opportunities like no other. Now, it depends upon your reasoning, whether you want to go for it or not. Considering all the issues of security in cloud computing.








.jpg)